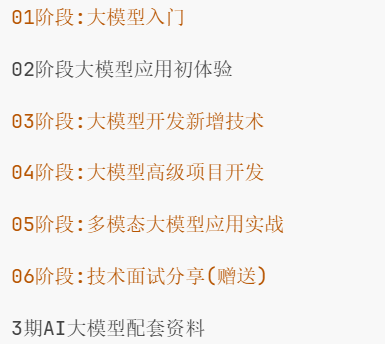
📁 二进制安全系列教程
📁 slides
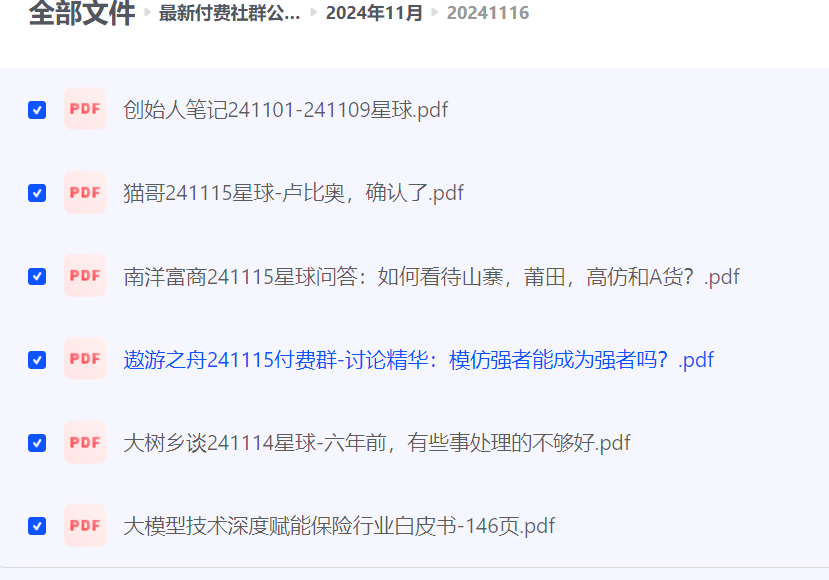
📁 0x0D Windows环境下的ROP(下)
📁 0x0E 探索上古Windows用户堆
📁 0x10 近代Windows用户堆的利用基础
📁 0x12 浅析Linux堆内存管理
📁 0x04 经典栈溢出实例之DNSTracer
📁 0x0C Windows环境下的ROP(上)
📁 0x09 Linux环境下的ROP(上)
📁 0x11 【特别篇】深入理解LFH
📁 0x0A Linux环境下的ROP(下)
📁 0x05 探索stack cookie
📁 0x08 DEP与ASLR简述
📁 0x07 一次失败的栈溢出(SEH)之GetGo Download Manager
📁 0x0B Linux下ROP练习之r0pbaby[CTF-2015-defcon]
📁 0x03 经典栈溢出实例之EasyRM2MP3
📁 0x01 经典栈溢出(上)
📁 0x02 经典栈溢出(下)
📁 0x0F 【特别篇】Windows上古-近代堆详述
📁 二进制安全(国外)
📁 0x06 另辟蹊径之覆盖SEH
📄 Linux环境下的ROP.pptx
📄 DEP & ASLR简述.pptx
📄 另辟蹊径之覆盖SEH.pptx
📄 探索Stack Cookie.pptx
📄 经典栈溢出.pptx
📄 探索上古Windows用户堆.pptx
📄 浅析Linux堆内存管理.pptx
📄 Windows环境下的ROP.pptx
📄 近代Windows用户堆的利用基础.pptx
📄 Windows环境下的ROP(下).mp4
📄 探索上古Windows用户堆.mp4
📄 近代Windows用户堆的利用基础.mp4
📄 Windows环境下的ROP(上).mp4
📄 Linux环境下的ROP(上).mp4
📄 经典栈溢出实例之DNSTracer.mp4
📄 浅析Linux堆内存管理.mp4
📄 Linux环境下的ROP(下).mp4
📄 DEP与ASLR简述.mp4
📄 【特别篇】深入理解LFH.mp4
📄 探索stack cookie.mp4
📄 Linux下ROP练习之r0pbaby[CTF-2015-defcon].mp4
📄 一次失败的栈溢出(SEH)之GetGo Download Manager.mp4
📄 经典栈溢出实例之EasyRM2MP3.mp4
📄 经典栈溢出(上).mp4
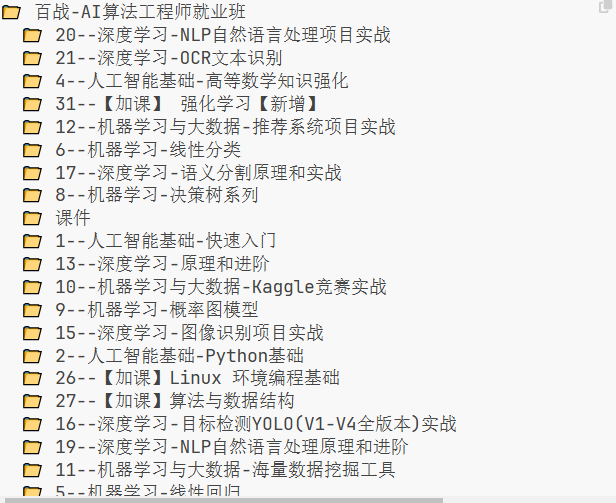
📁 Binary_Hacking_Course
📄 另辟蹊径之覆盖SEH.mp4
📄 经典栈溢出(下).mp4
📄 【特别篇】Windows上古-近代堆详述.mp4
📄 Writing a simple Program in Python – bin 0x03-ajy1PHWYeyQ.mkv
📄 Reversing and Cracking first simple Program – bin 0x05-VroEiMOJPm8.mkv
📄 The Heap – How to exploit a Heap Overflow – bin 0x15-TfJrU95q1J4.mp4
📄 Simple Tools and Techniques for Reversing a binary – bin 0x06-3NTXFUxcKPc.mkv
📄 heap0 exploit speedrun & weird ASCII string on the Heap – bin 0x28-fJMnH0kCAak.webm
📄 Global Offset Table (GOT) and Procedure Linkage Table (PLT) – bin 0x12-kUk5pw4w0h4.mkv
📄 Uncrackable Program Finding a Parser Differential in loading ELF – Part 2_2 – bin 0x08-OZvc-c1OLnM.mkv
📄 The Heap – Once upon a free() – bin 0x17-gL45bjQvZSU.mp4
📄 The Heap – dlmalloc unlink() exploit – bin 0x18-HWhzH–89UQ.mkv
📄 Adapting the 32bit exploit to 64bit for format4 – bin 0x27-_lO_rwaK_pY.mkv
📄 The Heap – what does malloc() do – bin 0x14-HPDBOhiKaD8.mkv
📄 [Live] Remote oldschool dlmalloc Heap exploit – bin 0x1F-2GVi8_9u5TY.webm
📄 Reverse engineering C programs – bin 0x10-vXWHmucgZW0.mkv
📄 Uncrackable Programs Key validation with Algorithm and creating a Keygen – Part 1_2 – bin 0x07-qS4VWL5R_OM.mkv
📄 Identifying another exploit mitigation and find bypass. stack0 – part 2 – bin 0x22-MMm0I2Dj51A.webm
📄 How a CPU works and Introduction to Assembler – bin 0x04-6jSKldt7Eqs.mkv
📄 First Stack Buffer Overflow to modify Variable – bin 0x0C-T03idxny9jE.mkv
📄 Rooting a CTF server to get all the flags with Dirty COW – CVE-2016-5195-Lj2YRCXCBv8.webm
📄 Playing around with a Format String vulnerability and ASLR. format0 – bin 0x24-CyazDp-Kkr0.mkv
📄 Linux signals and core dumps – bin 0x1C-_shKdU7mGxs.mkv
📄 Socket programming in python and Integer Overflow – bin 0x1B-d6BU8DWxb3c.mp4
📄 Developing an intuition for binary exploitation – bin 0x20-akCce7vSSfw.mkv
📄 TCP Protocol introduction – bin 0x1A-0EHo0HsTKJw.mkv
📄 The Heap – How do use-after-free exploits work – bin 0x16-ZHghwsTRyzQ.mp4
📄 First remote root exploit – bin 0x1D-HAN8Qun26cQ.mkv
📄 Format String Exploit and overwrite the Global Offset Table – bin 0x13-t1LH9D5cuK4.mkv
📄 Buffer overflow on a modern system impossible stack0 – part 1 – bin 0x21-4HxUmbOcN6Y.webm
📄 First Exploit! Buffer Overflow with Shellcode – bin 0x0E-HSlhY4Uy8SA.mkv
📄 First steps into networking with net0 from exploit.education protostar – bin 0x19-2CL-AAcgyuo.webm
📄 A simple Format String exploit example – bin 0x11-0WvrSfcdq1I.mkv
📄 Buffer Overflows can Redirect Program Execution – bin 0x0D-8QzOC8HfOqU.mkv
📄 Doing ret2libc with a Buffer Overflow because of restricted return pointer – bin 0x0F-m17mV24TgwY.mkv
📄 Writing a simple Program in C – bin 0x02-JGoUaCmMNpE.mkv
📄 LiveOverflow Channel Introduction and Backstory – bin 0x00-iyAyN3GFM7A.mkv
📄 Stack grooming and 100% reliable exploit for format0 – bin 0x25-AahpiYxKR2c.mkv
📄 Introduction to Linux – Installation and the Terminal – bin 0x01-navuBR4aJSs.mkv
📄 Bruteforce 32bit Stack Cookie. stack0 – part 3 – bin 0x23-KGzHcqJV-QM.mkv
📄 Syscalls, Kernel vs. User Mode and Linux Kernel Source Code – bin 0x09-fLS99zJDHOc.mkv
📄 Remote format string exploit in syslog() – bin 0x1E-MBz5C9Wa6KM.mkv
📄 format2 on a modern Ubuntu – bin 0x26-Kc6_PpdbcCw.webm
📄 The deal with numbers – hexadecimal, binary and decimals – bin 0x0A-mT1V7IL2FHY.mkv
📄 Smashing the Stack for Fun and Profit – setuid, ssh and exploit.education – bin 0x0B-Y-4WHf0of6Y.mkv
📄 Explaining Dirty COW local root exploit – CVE-2016-5195-kEsshExn7aE.mkv







暂无评论内容